FEATURED
-

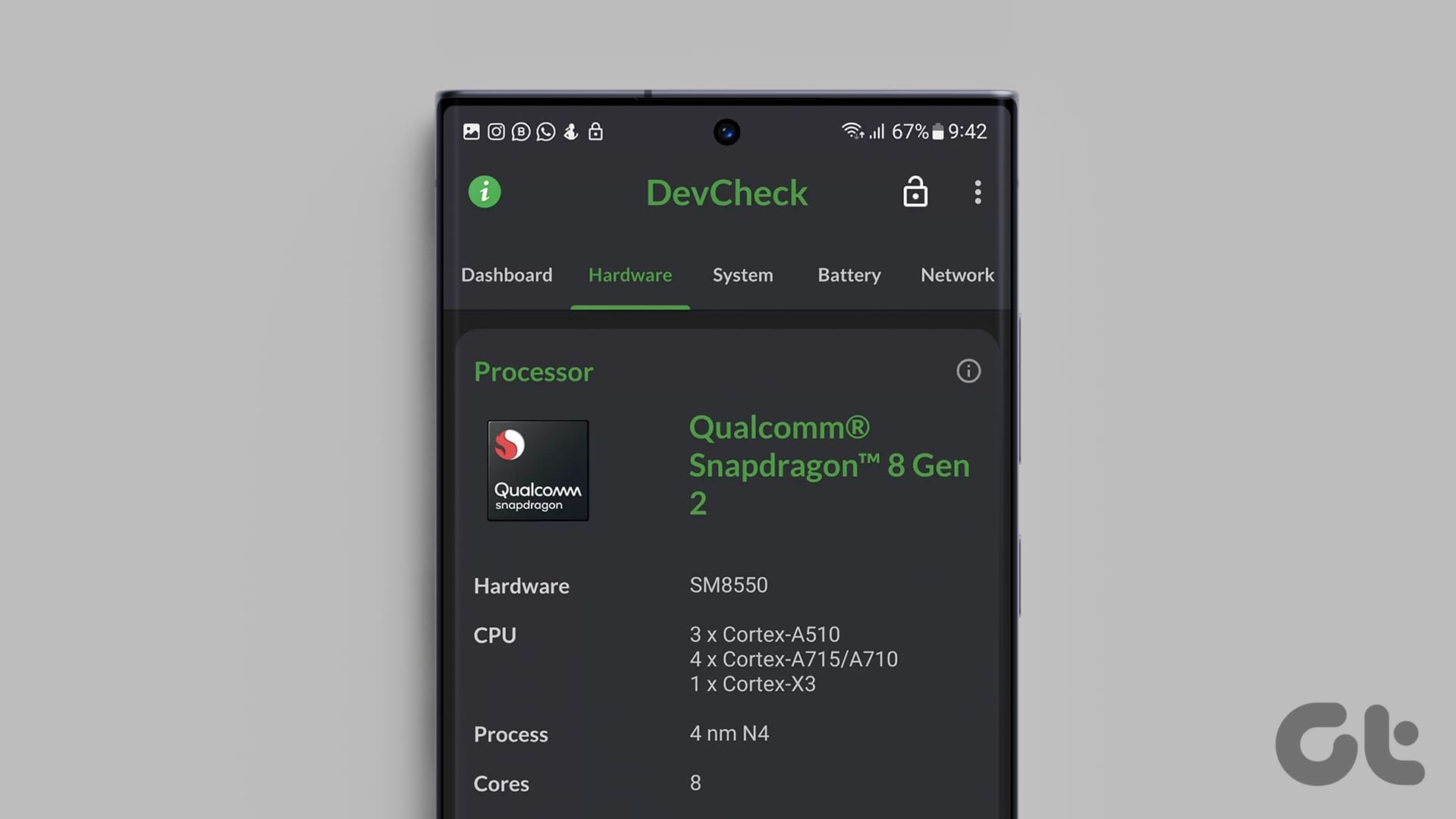
How to Check Processor on Your Android Phone (Including Samsung)
Unsure what processor your device currently has? Here are 4 ways you can use to check the processor on your Android phone.
-

How to Put Different Headers and Footers on Different Pages in Word
Easily customize your document layout by learning how to put different headers and footers on different pages in Word.
Recommended
latest
-

How to Find IMEI Number on Android (With/Without Phone)
Let us look at 7 ways you can use to find the IMEI number of your Android phone, regardless of whether you have the device or not.
More Latest Articles
-

6 Best Ways to Fix Apple TV Stuck on Apple Logo
Apple TV getting stuck at the Apple logo can spoil your ideal streaming setup. Check the top ways to troubleshoot the problem.
-

3 Best Ways to Record Audio on Mac
Here’s how you can record audio on your Mac using built-in tools. We will also share the steps to record your Mac screen with audio.
-

5 Easiest Ways to Transfer Files From iPhone to Mac
Need to transfer files, photos, or videos from your iPhone? Explore these five easiest ways to transfer files from your iPhone to a Mac.